Server Name Indicator (SNI) on NLB Demo
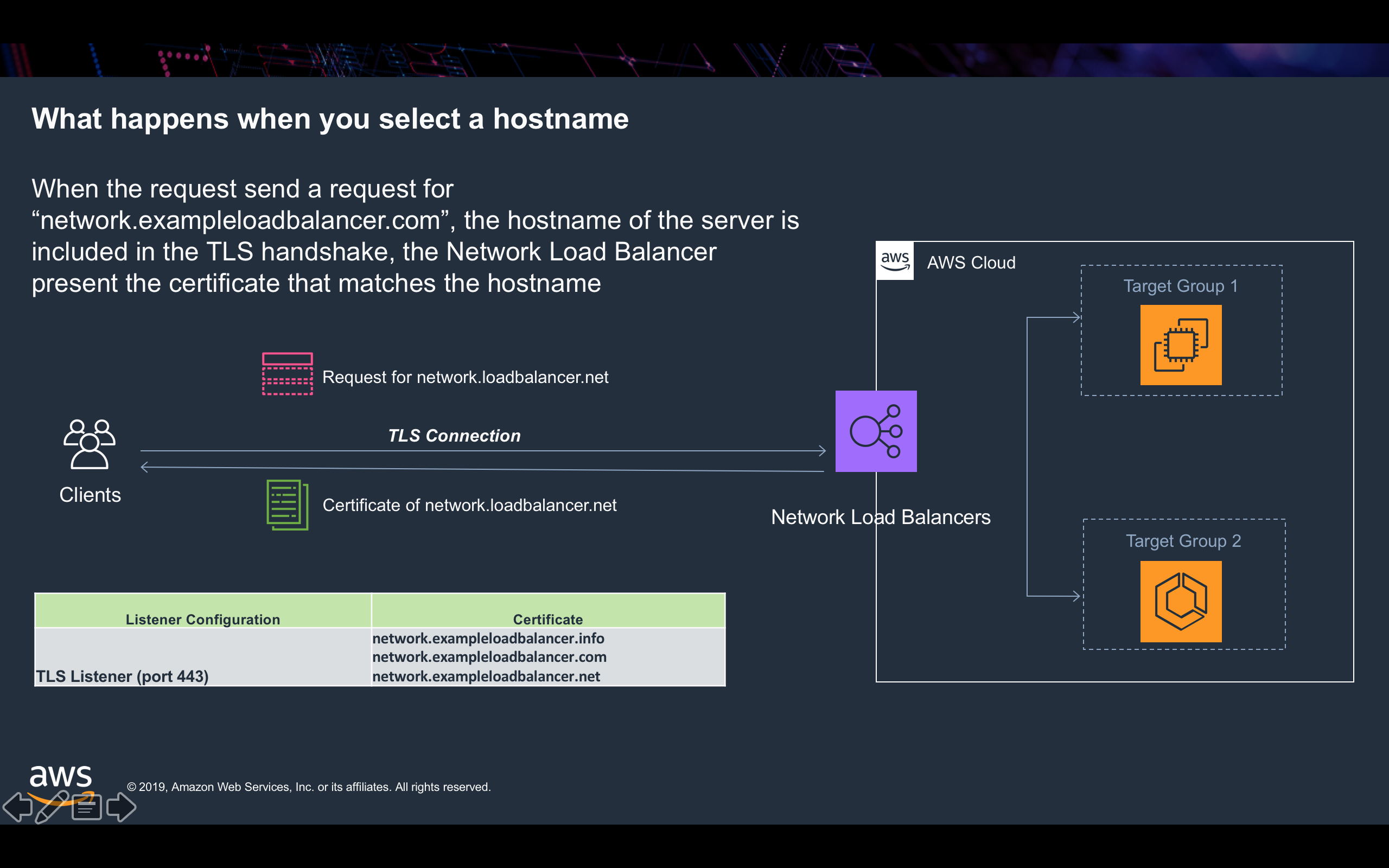
Server Name Indication (SNI) is an extension to the Transport Layer Security (TLS) computer networking protocol by which a client indicates which hostname it is attempting to connect to at the start of the handshaking process.
You can verify that the name on the cert is the same as the site name, and the only cert served. Change hostname and you'll get a different cert. Hostnames other than www will use the wildcard cert, so you'll see an * as the hostname.
This site is hosted behind an Network Load Balancer and is using Server Name Indication (SNI).
This allows it to serve multiple, independent, TLS certificates based on the hostname indicated by clients.
It's a few simple web pages hosted on servers in EC2 running Nginx behind and NLB. The real fun is nothing magical, just changing which certificate is provided based on what you try to connect to.
NLB uses Smart Certificate Selection to choose the best certificate whenever there are multiple matches.
You can use SNI on your NLB today, just add more certificates in the console!
The table below shows you the certificate used by this Network Load Balancer. Use the drop down menus below to explore links to different Fully Qualified Domain Names (FQDNs) that SNI is configured for on the Network Load Balancer. When you select a domain name, for example, "network.exampleloadbalancer.com", the Network Load Balancer selects the certificate of "network.exampleloadbalancer.com" for the TLS connection and present its certificate information in the table below.
Different Top Level Domains Names
The menu below includes all the static domain names with different different Top Level Domains (TLD - we have 3 on this site, exampleloadbalancer.[com|net|info]).
Wildcard and Random Prefix Domain Names
The menu below includes the domains with random prefixes and .net Top Level Domain. As you can see, Network Load Balancer selects wildcard.* for the random requested domain names.
Certificate Information
SerialNumber:08:55:3f:6b:0c:b7:9a:9c:f2:c3:d0:4f:42:41:bf:80
Subject:CN=www.exampleloadbalancer.net